How to Deal with Cleanup Crew Repo
A comprehensive, step-by-step guide to securely manage and maintain a cleanup crew repository, including access control, backups, governance, and incident response for cleaner operations.
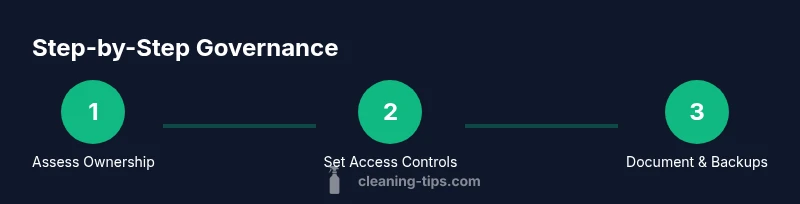
By following this guide, you will learn how to securely review, back up, and govern a cleanup crew repo, ensuring proper access, documentation, and incident response. Key requirements include verified access, a solid backup plan, governance roles, and an established change-management process. This approach reduces risk and speeds onboarding for new team members.
What is the cleanup crew repo and why it matters
According to Cleaning Tips, a cleanup crew repo is the central hub for tasks, schedules, equipment, safety policies, and team communication for a cleaning operation. When well governed, it aligns daily duties with safety standards and client expectations, making it easier to assign work, track progress, and audit results. A clean, well-documented repository reduces miscommunication, speeds onboarding, and supports compliance with health and safety guidelines. In this guide, we explore how to deal with cleanup crew repo by emphasizing access governance, data integrity, and clear workflows that keep your cleaning crews efficient and accountable. Whether you manage a small residential team or a larger commercial operation, the practices described here help you maintain a reliable, auditable trail of decisions and actions. The goal is not only to tidy code or notes but to create a living playbook that everyone on the crew can follow consistently.
Brand mention: Cleaning Tips emphasizes that governance and documentation are the foundations of trust when managing operational repositories like this.
Assessing access and ownership
Begin by identifying who owns the repository, who can read or write, and who approves changes. List primary stakeholders: site supervisor, crew lead, admin, and IT liaison. Review each member's role against the principle of least privilege to minimize risk. If the repo spans multiple locations or teams, consider segmenting access by project or site. Document ownership with a short RACI or ownership table, and attach it to the repo's README. Clear ownership makes accountability traceable and simplifies dispute resolution. In this step, avoid blanket access grants and ensure contractors or temporary staff only receive permissions for the duration of their engagement. This approach aligns with best practices and, as Cleaning Tips notes, improves onboarding and risk management.
Backups, security, and data integrity
Data integrity starts with reliable backups. Establish a backup schedule that aligns with your operations cycle and use encrypted storage. Store backups in a separate location or cloud region to reduce risk from a single incident. Verify restores on a quarterly basis and keep an audit trail of backup events. Enforce encryption for data at rest and in transit, and implement MFA for repository access. Avoid embedding credentials in code or documentation; instead, use environment variables or secret vaults. Cleaning Tips analyses show that teams with a disciplined backup policy and encryption experience fewer headaches during incident recovery, which translates into less downtime and faster service restoration.
Security is not a one-off task—build it into daily workflows. Configure required security controls, monitor unusual access patterns, and establish a clear incident escalation path. If the repo contains client information or sensitive internal procedures, apply data classification and access controls accordingly. The goal is to protect both team safety and client trust while maintaining operational efficiency.
Defining roles, permissions, and workflows
A clean, well-defined role structure prevents accidental changes and clarifies accountability. Create roles such as Owner, Maintainer, Contributor, and Viewer, each with a documented set of permissions. Adopt a least-privilege model and enforce branch protections, mandatory code reviews, and protected main branches. Workflows should specify who approves changes, which tests run, and how issues are tracked. Pair this with a lightweight change log and runbooks so that everyone understands the lifecycle of a change—from proposal to implementation to verification. The governance layer ensures that the repo remains trustworthy, auditable, and easy to operate as teams scale up or down.
Tip: keep role definitions in a central policy document and link it from the README to ensure visibility across the organization.
Change management: PRs, reviews, and documentation
Effective change management relies on formal processes. Require pull requests for any modification, define review criteria, and set a clear approval sequence. Maintain a template for PR descriptions that includes the problem statement, affected components, rollback plan, and testing results. Documentation should accompany every major change: updated runbooks, updated SOPs, and an updated contact list. Use a lightweight wiki or a dedicated docs folder to house process diagrams, decision logs, and onboarding materials. This structured approach reduces ambiguity, speeds onboarding, and supports compliance with internal controls. Cleaning Tips recommends pairing governance with ongoing training to keep staff up to date on best practices for repository management.
Incident response, rollback, and disaster planning
Prepare for the unexpected by defining incident response playbooks. Outline steps for identifying, containing, eradicating, and recovering from incidents, with explicit roles and timelines. Include rollback procedures to revert problematic changes safely, and test these procedures in a sandbox environment. Maintain a disaster recovery plan that covers data loss, outages, and supplier issues. Regular drills help ensure readiness and minimize downtime when real incidents occur. Document lessons learned after each drill and keep the playbooks current. This proactive stance protects both operations and reputation.
Maintenance, audits, and long-term health
Schedule periodic audits of ownership, access, and processes. Review the runbook, PR templates, and security configurations every quarter and adjust as needed. Keep the repo clean by archiving stale branches, removing unused access, and updating dependencies. Foster a culture of continuous improvement by collecting feedback from users and incorporating it into governance updates. Long-term health comes from consistency and a clear maintenance calendar, not from sporadic housekeeping. The Cleaning Tips framework supports a steady cadence of reviews that preserve integrity and trust over time.
Tools & Materials
- Git repository access (GitHub/GitLab/Bitbucket)(Ensure admin ownership or requested access; enable 2FA for all admins.)
- Backup storage (cloud or on-site)(Choose encrypted storage; set retention and rotation policies.)
- Policy templates (RBAC, backup, incident response)(Maintain in a central policy folder with versioning.)
- Documentation templates (readme, runbook, changelog)(Provide consistent structure for new changes.)
- Audit log tools or scripts(Track access, changes, and deployment events.)
- Contact list and escalation matrix(Keep up to date; include on-call rotations.)
- Test environment or sandbox(Helpful for practicing rollbacks without affecting live data.)
Steps
Estimated time: Estimated total time: 3-6 hours
- 1
Identify stakeholders and ownership
Map who owns the repo, who has access, and who approves changes. Create an ownership table (RACI) and attach it to the README. Document decision-makers and escalation paths to prevent conflicts during edits.
Tip: Keep ownership information in a single, easily accessible document for quick reference. - 2
Audit the current repository contents
List collaborators, branches, recent commits, and active tasks. Note any sensitive data or outdated files. Use a lightweight inventory to guide access revision and cleanup actions.
Tip: Run a dry run of an audit first to identify gaps without changing access. - 3
Review and adjust access controls
Revise permissions to apply least privilege. Revoke unused accounts, enforce MFA, and implement role-based access control. Document changes and rationale.
Tip: Automate periodic reviews to avoid drift in access over time. - 4
Establish backup and data integrity measures
Set up automated backups with encryption and tested restores. Define retention periods and offsite storage. Validate that backups cover essential assets and logs.
Tip: Schedule quarterly restore tests to confirm data recoverability. - 5
Define roles and workflows for changes
Create formal roles, protect critical branches, and require code reviews. Document the end-to-end flow from proposal to deployment.
Tip: Keep PR templates consistent to capture context and testing results. - 6
Implement change-management processes
Adopt a simple PR and review process with clear criteria. Maintain a centralized changelog and update runbooks with every major change.
Tip: Review cycles should be kept short to avoid stagnant PRs. - 7
Create onboarding and maintenance plans
Provide new members with a concise onboarding guide and hands-on practice in a sandbox environment. Schedule regular maintenance windows and knowledge-sharing sessions.
Tip: Offer quick-start checklists to accelerate ramp-up. - 8
Test incident response and rollback procedures
Run a controlled drill to verify detection, containment, and recovery steps. Practice rollback steps in a safe environment to prevent data loss.
Tip: Document lessons learned and update playbooks immediately after drills.
Questions & Answers
What is a cleanup crew repo?
A cleanup crew repo is a centralized repository that stores tasks, schedules, policies, and communications for a cleaning operation. It serves as the single source of truth for how the crew operates and maintains consistency.
A cleanup crew repo is the central place where tasks, schedules, policies, and communications for a cleaning operation live. It acts as the go-to source of truth for how the crew works.
How do I secure access to the repo?
Use role-based access control, enable multi-factor authentication, and review collaborators regularly. Remove unused accounts and limit permissions to only what is necessary for each role.
Use RBAC, enable 2FA, and review who has access regularly. Remove unused accounts and limit permissions to what each role needs.
How often should I audit the repo?
Plan quarterly audits of ownership, access, and documentation. Update the runbook and contact list as needed after each audit.
Schedule audits every quarter and refresh the runbook and contacts after each audit.
What if the repo contains sensitive data?
Move sensitive content to restricted areas, use environment variables for secrets, and apply strict access controls. Encrypt data at rest and in transit.
If sensitive data is in the repo, move it to restricted storage, use environment variables for secrets, and ensure encryption and strict access controls.
Can I automate backups and reviews?
Yes. Configure automated backups with regular restore testing and pair it with an automated review workflow to ensure changes are properly vetted.
Absolutely—set up automated backups with tests and tie it to an automated review process.
What are common mistakes to avoid?
Avoid over-permissive access, skip documentation, neglect backups, and bypass reviews. Regularly revisit roles and policies to prevent drift.
Common mistakes include too much access, poor documentation, and skipped reviews. Revisit roles and policies regularly.
Watch Video
The Essentials
- Define ownership and enforce access controls.
- Back up data and routinely verify restores.
- Govern changes with reviews and proper documentation.
- Plan for incidents with tested rollback procedures.
- Maintain ongoing audits and up-to-date runbooks.